HackTheBox - CCTV
先修改WSl和Windows的/etc/hosts
基本Recon
1 | |
Directory Scanning / Subdomain Enumeration也都沒有什麼問題,所以就直接從front page source code去看,發現他有一個login page: /zm,這是ZoneMinder的產品,下意識想找version再從CVE去找,但沒啥結果,想說應該也會有SQLi,也沒有明顯的info leak,後來想說default password可以試看看: admin:admin居然被我賽中了
從後台撈資料
- Version:
1.37.63→ 比較新的version,重大的漏洞都patch了 - Log:
- authentication:
/usr/share/zoneminder/www/includes/auth.php - 可能有用的東西:
'zmfilter.pl --filter_id=1 --daemon' started at 26/03/25 07:58:31
- authentication:
- Users:
- admin
- mark
- superadmin
- Storage:
/var/cache/zoneminder/events
1 | |
- Username:
mark - Password:
opensesame
提權
1 | |
比較常見的port是
1 | |
我們要看的是那些不常見的
1 | |
感覺:8765和:7999是個網頁,而且只允許localhost query,那麼我們可以透過ssh tunnel建立連線,也就是我們自己的host → ssh → localhost:8765也就是local port forwarding
1 | |
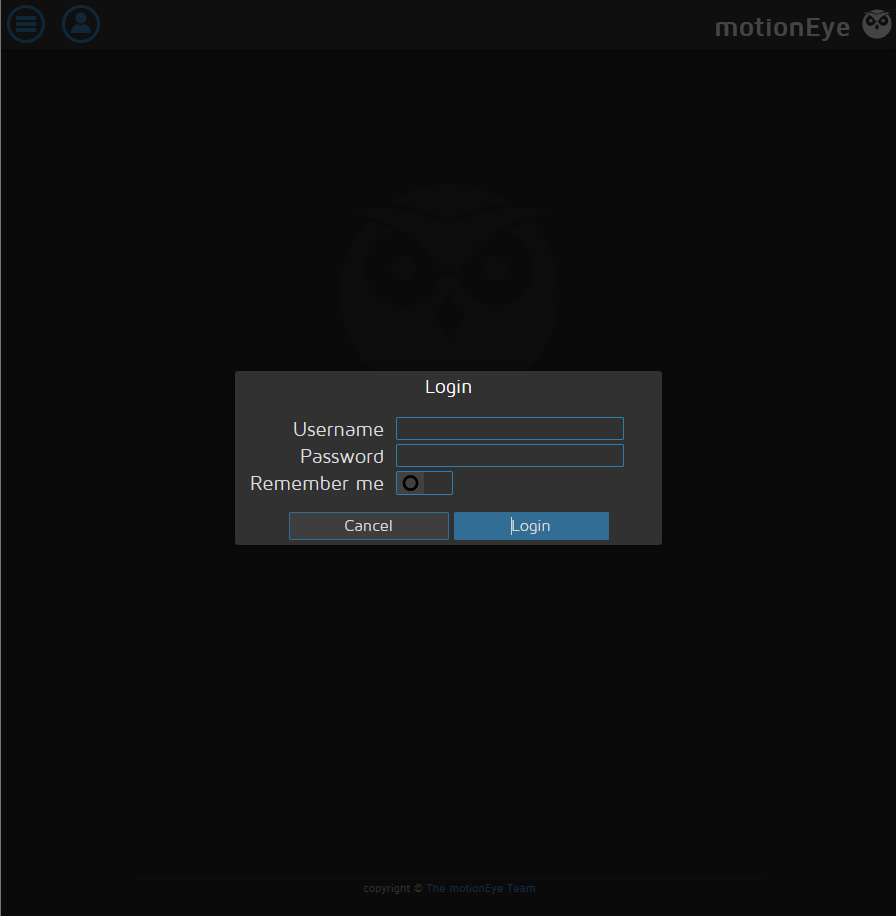
在本機request 127.0.0.1:8765會發現
 根據官方的README(motioneye-project/motioneye)
根據官方的README(motioneye-project/motioneye)
motionEye is an online interface for the software motion, a video surveillance program with motion detection.
另外根據motion官方的page(motion project)
Motion is a highly configurable program that monitor video signals from many types of cameras and depending upon how they are configured, perform actions when movement is detected.
也就是說,motioneye是一個前端的console介面,實際在後端運行camera daemon的是motion,而如果是只有motioneye的話應該只會有:8765,但看到有:7999那就代表HTB已經先幫我們註冊了一個camera,所以才會跑motion daemon,這個在後面會很重要,一樣先看有沒有對應的CVE,目前motioneye的版本為0.43.1b4,在motioneye的登入畫面source code可以看到,然後可以對應到CVE-2025-60787,並且看了一下發現的網友的wp: MotionEye RCE via Client-Side Validation Bypass,但是這是一個需要motioneye的帳號密碼
通常motioneye的config會寫在/etc/motioneye/motion.conf
1 | |
- Username:
admin - Passowrd:
989c5a8ee87a0e9521ec81a79187d162109282f0
這樣就可以找有沒有對應的poc: CVE-2025-60787 - Authenticated RCE in motionEye
1 | |
另外一個terminal如下
1 | |
- User Flag:
2678adb968a3f49e749f876ef4092e81 - Root Flag:
2cac047cd0eb7335f4b212531260cf5d
最後的這個攻擊之所以會成功是因為HTB已經先幫我們註冊了一個camera daemon,讓poc可以針對這個daemon做一些api上的command injection操作,如果是沒有註冊任何camera daemon,在poc打payload之前就會報error,畢竟poc真正在打的是:7999這個服務,換言之,既然都是直接打:7999這個服務,那是不是就沒必要得到motioneye的帳密呢?我只要針對:7999送query就好啦,詳情可以看【滲透測試】HTB Season 10 CCTV 全過程WP
1 | |