HackTheBox - Facts
Port Scanning & Subdomain Enumeration & Directory Scanning
開80, 22 port,但好像沒有subdomain
1 |
|
透過爆破directory可以發現登入頁面,而且還得知CMS第三方的軟體: Camaleon 2.9.0
找CVE
A Privilege Escalation through a Mass Assignment exists in Camaleon CMS When a user wishes to change his password, the ‘updated_ajax’ method of the UsersController is called. The vulnerability stems from the use of the dangerous permit! method, which allows all parameters to pass through without any filtering.
這個PoC蠻好用的: CVE-2025-2304 - Camaleon CMS Privilege Escalation,我們先隨便註冊一個user,並且用這個poc提權
1 |
|
此時回到登入頁面會發現我們已經變成admin
撈資料
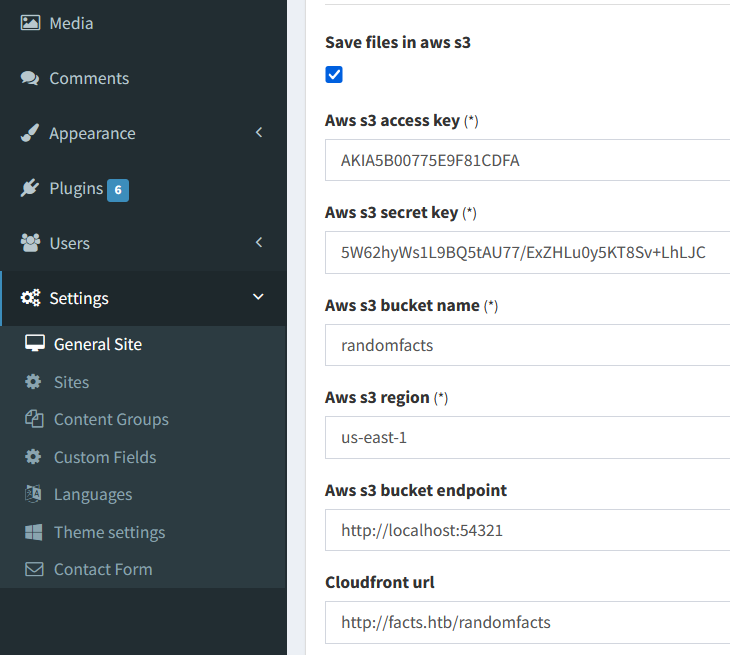
在後台(http://facts.htb/admin/settings/site)可以確認幾件事情
- 他有使用AWS S3並且開在
localhost:54321 - Access Key:
AKIA198F92999486AEF5 - Secret Key:
JiRzv8R1uS3hzeMkKTuC9/qr+MKCTq8NGvZw3NGa
連線S3 Dump SSH
因為沒有用過AWS所以要先install
1 |
|
爆破ssh
以下都是在Kali中完成
1 |
|
現在的問題點是不知道username,逛了好久都沒有什麼收穫,於是又上網看了一圈CVE發現雖然CVE-2024-46987官網限定2.8.0 < 2.8.2但不知道為什麼也同樣可以使用在2.9.0 - CVE-2024-46987 - Camaleon CMS Authenticated Arbitrary File Read
This Python PoC exploits CVE-2024-46987, a Path Traversal bug in Camaleon CMS 2.8.0 < 2.8.2 (work on 2.9.0). It allows authenticated users to read sensitive server files via the MediaController. Intended for authorized security auditing and educational research only.
1 |
|
終於找到username和user.txt
提權
先recon一下發現我們可以root使用facter,上網搜了一圈發現提權非常簡單
1 |
|
另外一個terminal
1 |
|
- User Flag:
98123feb252b2d8094d6508f790d9972 - Root Flag:
274dce2b303311d57158cb9020ff6271