HackTheBox - Principal
Port Scanning & Directory Scanning
1 | |
Bypass JWT
這題是 classic JWT misconfiguration,正常的流程可以看Security Related,後端parser header之後發現alg為none並且沒有signature,正常的server應該要reject,但他完全沒驗證signature就相信payload我是admin
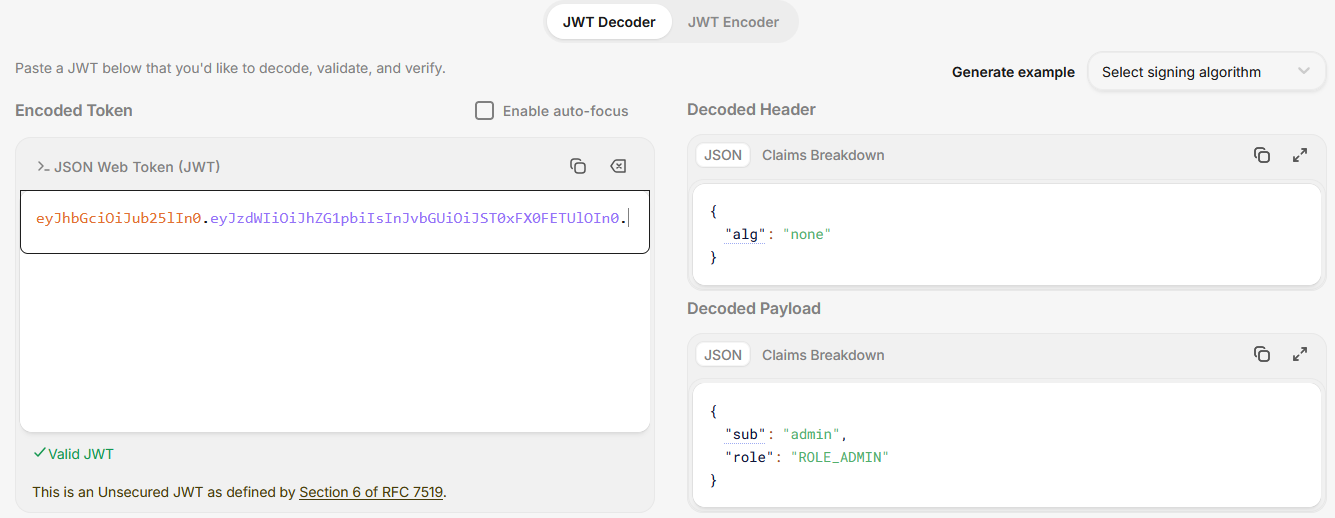
並且這一題還有提到JWE,正常流程應該:
- 解密 JWE
- 取出 JWT
- 驗證 signature
但這台直接接受 plaintext JWT,所以我們同時bypass JWE和JWT
存取API
1 | |
1 | |
這邊的重點是
1 | |
所以大膽猜可能有password reuse的問題
1 | |
提權
繼續在API中撈資料並且看一下有哪些可以用的資訊
1 | |
1 | |
從上述的repsonse中,可以發現以下關鍵訊息
1 | |
代表系統會:
- 發 SSH certificate
- 給 svc-deploy 用
- 用 CA 簽章
而且前面都有提到CA在/opt/principal/ssh/,那麼我可以把CA dump到local,然後自己產生key再用CA簽章,最後用Root的身份進去,完成提權
1 | |